Induct For Work online induction system admin users can activate an optional security add on called 2FA. But what is it? And how does it work?
What is Two-Factor Authentication?
In an era where digital security is paramount, Two-Factor Authentication (2FA) has emerged as a crucial layer of protection against cyber threats. This article dives into the concept of 2FA, its importance, how it works and its implications in the digital world.
Understanding Two-Factor Authentication
Two-Factor Authentication is a security process in which users provide two different authentication factors to verify themselves. This method adds an extra layer of security to the standard password method of online identification. In a world where personal and financial information is increasingly stored and managed online, the traditional single-password system has proven insufficient in protecting against unauthorized access, leading to a rise in the adoption of 2FA.
The Importance of 2FA

With cybercrime on the rise, the limitations of simple password protection have become glaringly obvious. Passwords can be guessed, cracked, or stolen, making them a weak single line of defense. 2FA addresses this vulnerability by requiring a second factor, which significantly decreases the likelihood of unauthorized access, even if the password is compromised.
How Two-Factor Authentication Works
Two-Factor Authentication involves combining two different types of credentials:
- Something You Know: This is typically the password or PIN, a piece of information that the user knows.
- Something You Have or Are: This could be a mobile device (something you have) where a user receives a text message with a code or uses an authentication app. Alternatively, it could involve biometrics (something you are), such as a fingerprint or facial recognition.
Types of Two-Factor Authentication
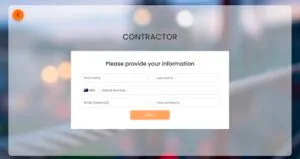
- SMS-Based 2FA: This involves sending a code via SMS to the user’s phone, which they then enter on the website or app. Induct For Work uses SMS based 2FA.
- Authentication Apps: Apps like Google Authenticator or Authy generate time-sensitive codes that users enter during the login process.
- Biometric Verification: This includes fingerprint scanning, facial recognition, or voice identification, leveraging unique biological traits as a form of authentication.
- Physical Tokens: Some systems use physical devices, like a key fob, which generates a code for the user to enter.
Advantages of Two-Factor Authentication
- Enhanced Security: By adding a second layer of security, 2FA makes it significantly harder for attackers to gain access to a person’s devices or online accounts.
- Reduced Fraud and Identity Theft: 2FA helps in reducing cases of online identity theft and fraud, as the second factor usually involves something that is physically possessed by the user.
- User Peace of Mind: For users, knowing that their accounts are better protected offers peace of mind, especially where sensitive financial or personal information is involved.
Challenges and Considerations
While 2FA adds an essential security layer, it’s not without challenges:
- User Inconvenience: Some users find 2FA processes cumbersome, particularly if it involves waiting for SMS codes or using an additional device.
- Dependence on Secondary Devices: In cases where the second factor involves a physical device or phone, losing or damaging this device can lock users out of their accounts.
- Vulnerabilities: Methods like SMS-based 2FA have their vulnerabilities, including the risk of interception or SIM swapping attacks.
The Future of Two-Factor Authentication
As cyber threats evolve, so do authentication methods. Future advancements in 2FA are likely to focus on ease of use and increased security measures, potentially incorporating more advanced biometrics and AI-driven authentication methods.
Final Words
Two-Factor Authentication represents an essential step forward in digital security. By requiring a second form of verification, 2FA substantially enhances protection against unauthorized access, making it a critical tool in safeguarding digital identities and sensitive data. As the digital landscape continues to evolve, the role of 2FA in security protocols is set to become even more prominent, adapting to new challenges and technological advancements.
If you would like to find out how to activate 2FA for your admin users please contact our sales team here, or talk to your Customer Success Manager.